Blog
Your blog category
Let’s Understand SOC and SOC as service. What should you look for a while opting SOC as service providers
𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗼𝗽𝗲𝗿𝗮𝘁𝗶𝗼𝗻𝘀 𝗰𝗲𝗻𝘁𝗲𝗿, 𝗼𝗿 𝗦𝗢𝗖, is a facility where a team of IT security experts monitors, detects, analyzes, and investigates
The Business Case for SASE: Cost Savings and Operational Efficiency
Consolidation of Network and Security Services: One of the primary benefits of implementing SASE is the consolidation of network and
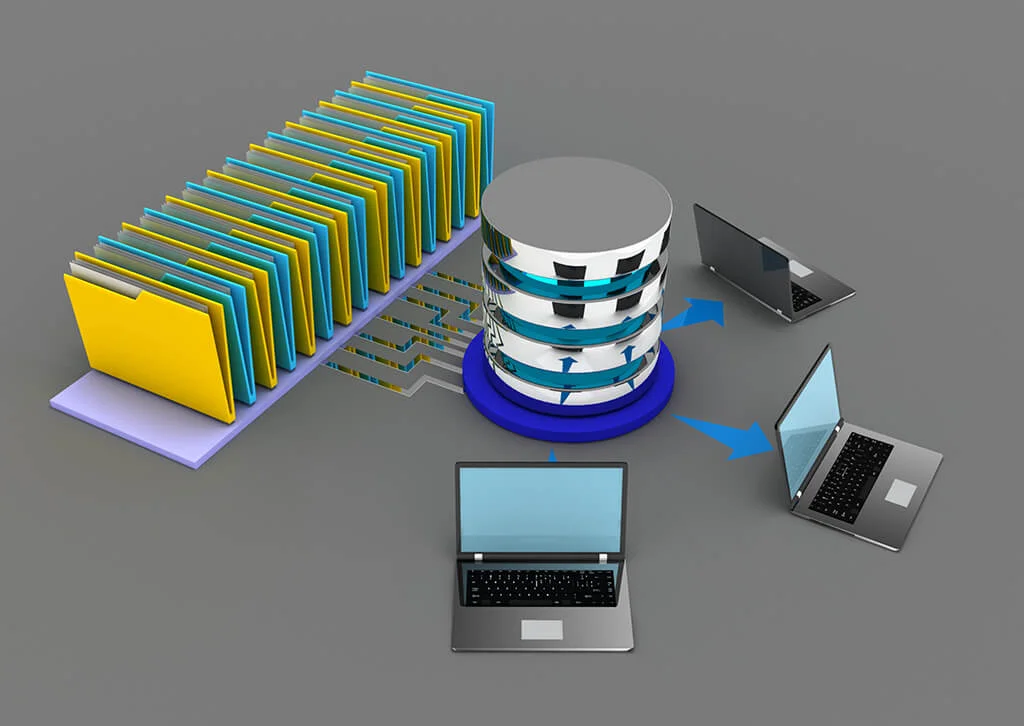
What is Object Storage?
There are three types of traditional object storage server File Storage File storage exists in two forms: File Servers and
SIEM, SOC and MDR are related but distinct concepts in the field of cybersecurity. Here’s a brief explanation of each and their differences:
SIEM (Security Information and Event Management) : SIEM is a technology solution that collects and analyzes security event data from
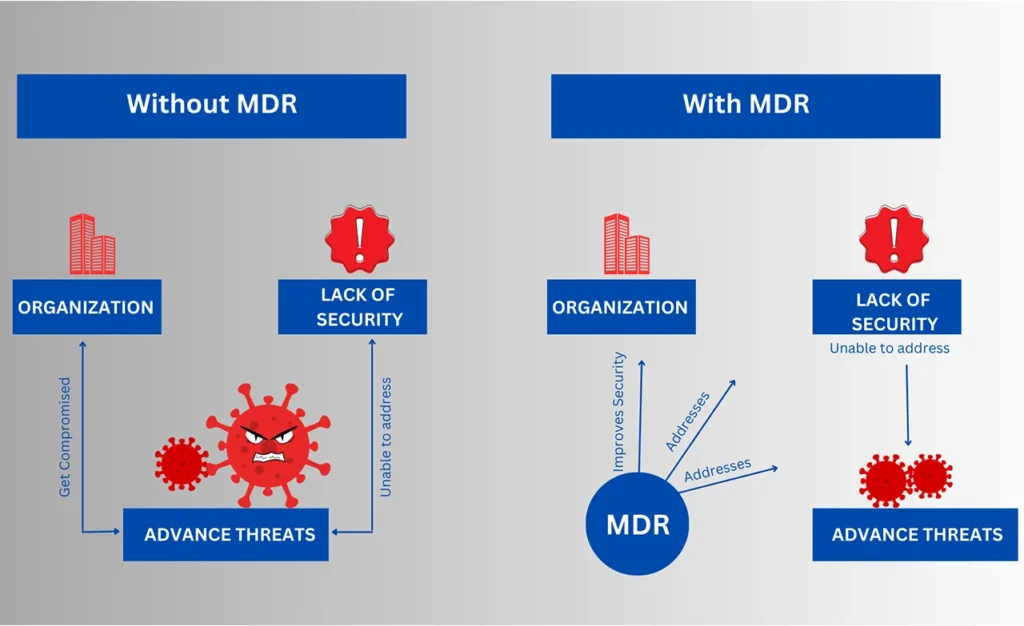
How MDR (Managed Detection and Response) is adding value to organizations?
MDR (Managed Detection and Response) provides great value to organizations by helping to identify and respond to cyber threats more
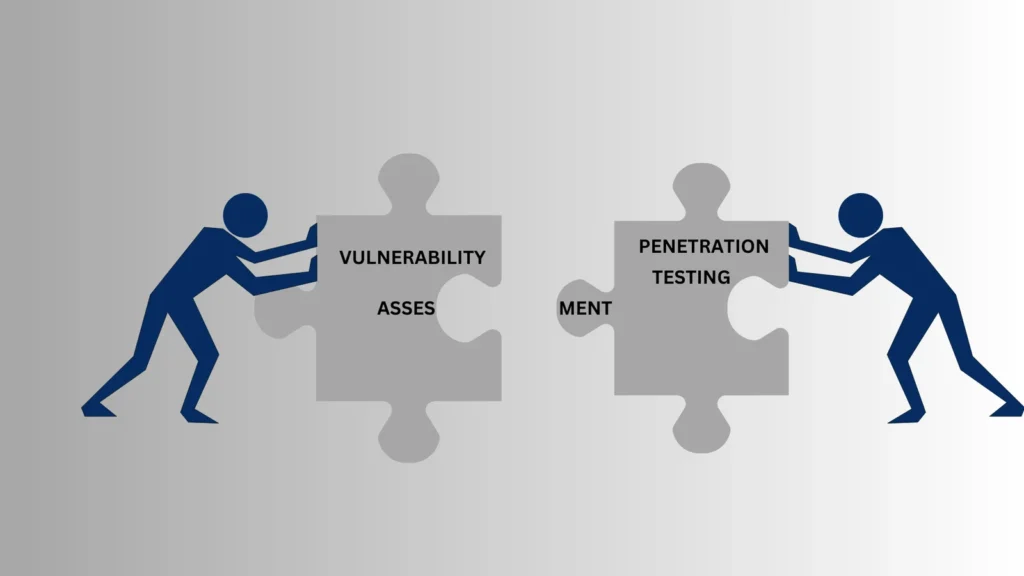
A Comprehensive Guide to VAPT: Safeguarding Your Business
Cybersecurity is a top concern for businesses of all sizes due to the rising number of cyberattacks. To safeguard sensitive